I'm always excited to take on new projects and collaborate with innovative minds.
Lagos
I'm always excited to take on new projects and collaborate with innovative minds.
Lagos
How Hackers, APTs & Red Teamers Weaponise Azure AD's Own Infrastructure Against You.
If you missed Part 1 — go read it first. This one hits harder. Here
We talked about how Microsoft's public Azure AD endpoints serve a legitimate purpose. Now let's talk about what happens when adversaries find them first.
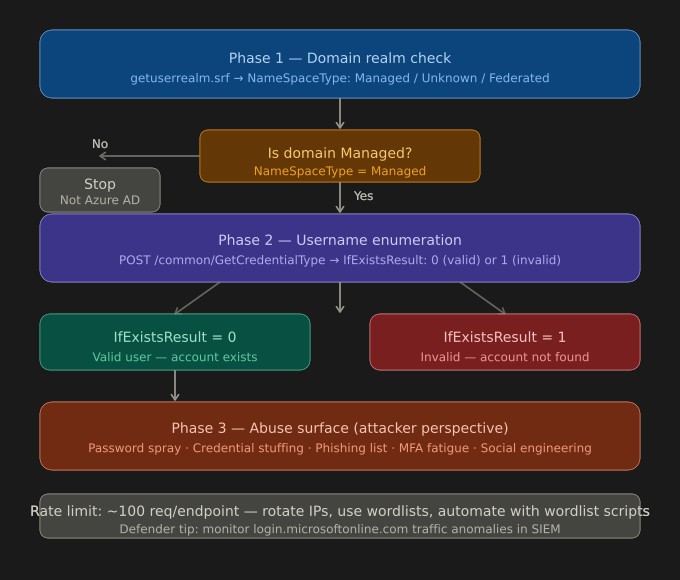
The attacker queries the getuserrealm endpoint against your domain. No authentication. No credentials. No logs on your side (by default).
In seconds they know:
→ Is your domain on Azure? Federated? Managed?
→ What's your federation provider? (Okta? ADFS? Ping?)
→ What's your cloud issuer URI?
This is OSINT with Microsoft's own infrastructure as the oracle.
If your domain is Managed — the game begins.
Attackers build a wordlist using:
They script the GetCredentialType endpoint:
→ Send username → Get IfExistsResult
→ 0 = Valid user. Add to list. Continue.
→ 1 = Invalid. Move on.
With 500 common employee name combinations, they can validate dozens of real accounts — silently, with no failed login attempts, and no MFA triggered.
🔇 Zero noise. Zero alerts. Zero lockouts.
This is why it's so dangerous — it doesn't look like an attack. It looks like normal Microsoft authentication traffic.
Groups like APT29 (Cozy Bear), APT33, and Scattered Spider have been documented using Azure AD enumeration as part of their initial access playbooks.
Here's the real-world attack chain:
The username list from Step 1? That's the seed that grows into a breach.
In authorised red team engagements, this technique is used to:
• Map the entire identity surface of a target org before touching any system
• Identify high-value targets (CEO, CFO, IT Admin accounts) for spear-phishing
• Build realistic attack simulations that mirror actual APT behaviour
• Test whether the blue team can detect enumeration activity at the network/identity layer
The fact that this requires ZERO authentication and generates MINIMAL logs makes it one of the most underestimated pre-attack techniques in enterprise environments.
1️⃣ Enable Microsoft Entra ID Identity Protection
Monitor for unfamiliar sign-in properties and atypical travel signals — even pre-auth anomalies.
2️⃣ Deploy Conditional Access Policies
Require compliant devices and block legacy authentication protocols that bypass modern controls.
3️⃣ Monitor Azure Sign-In Logs Aggressively
Filter for high-volume requests to /common/GetCredentialType from single IPs or unusual geolocations.
4️⃣ Implement Smart Lockout + Password Spray Detection
Azure AD Smart Lockout helps, but pair it with Microsoft Sentinel analytics rules for spray pattern detection.
5️⃣ Harden Your Public Footprint
Audit what employee emails are publicly exposed. LinkedIn, company websites, and press releases are attacker wordlists in disguise.
6️⃣ Enforce Phishing-Resistant MFA
Even if an attacker enumerates and obtains credentials — FIDO2 / Passkeys make stolen passwords useless.
7️⃣ Conduct Regular Red Team Exercises
The only way to know if your detections work is to test them — with permission, with scope, with purpose.
The same API Microsoft built to make your login experience seamless is the same API adversaries use to map your organisation's identity infrastructure — silently, legally grey, and largely undetected.
Knowledge is your first line of defence.
If your security team doesn't know this technique exists — your adversaries already do.
Secure identities. Harden your tenant. Test your assumptions.
Your email address will not be published. Required fields are marked *