I'm always excited to take on new projects and collaborate with innovative minds.
Lagos
I'm always excited to take on new projects and collaborate with innovative minds.
Lagos
EVERY Security Pro Should Know This About Azure AD — And So Should Every Defender.
(Save this. Share this. Your team needs it.)
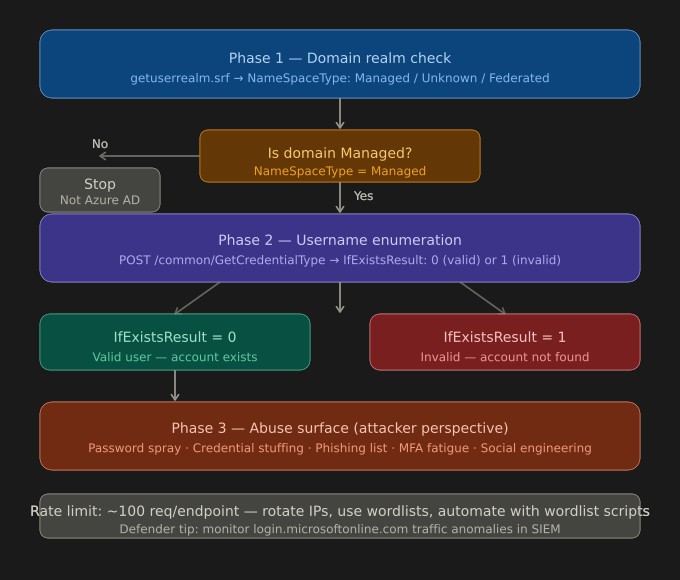
Before a red teamer fires a single payload, before a penetration tester touches a login page — there's a quiet, invisible phase happening against your organisation right now.
It's called Azure AD Reconnaissance. And it starts with a single HTTP request.
Microsoft exposes a public, unauthenticated endpoint:
🔗 https://login.microsoftonline.com/getuserrealm.srf
This endpoint was designed with a purpose — to allow Microsoft clients (Outlook, Teams, Office apps) to automatically discover how a domain is configured, so they can route authentication correctly.
The response tells you:
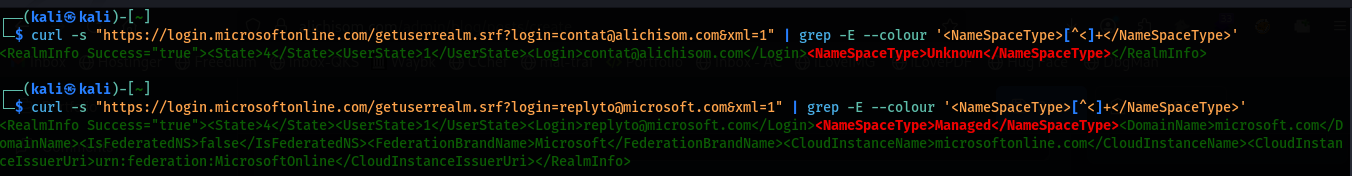
Example — checking a domain:
alichisom.com → NameSpaceType: Unknown (not on Azure)
microsoft.com → NameSpaceType: Managed (fully Azure AD managed)
For an IT admin, this is gold:
For a security engineer, this is your first stop in attack surface mapping.
Once you confirm a domain is Azure AD Managed, Microsoft exposes ANOTHER unauthenticated endpoint:
🔗 https://login.microsoftonline.com/common/GetCredentialType
Send a POST request with a username in JSON format — and the API returns an IfExistsResult value:
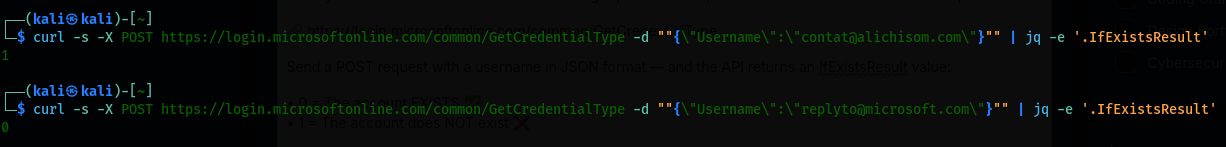
Legitimate uses:
This is the foundation of identity attack surface assessment. Knowing which accounts exist is step zero in understanding your exposure.
This endpoint is rate-limited to ~100 requests per session — but that's a soft guardrail, not a wall.
With a simple script, a wordlist of common usernames (firstname.lastname@company.com), and some patience — a lot can be discovered.
How threat actors, APT groups, and red teamers weaponise exactly this — and what your organisation MUST do to detect and defend against it.
Your email address will not be published. Required fields are marked *