I'm always excited to take on new projects and collaborate with innovative minds.
Lagos
I'm always excited to take on new projects and collaborate with innovative minds.
Lagos
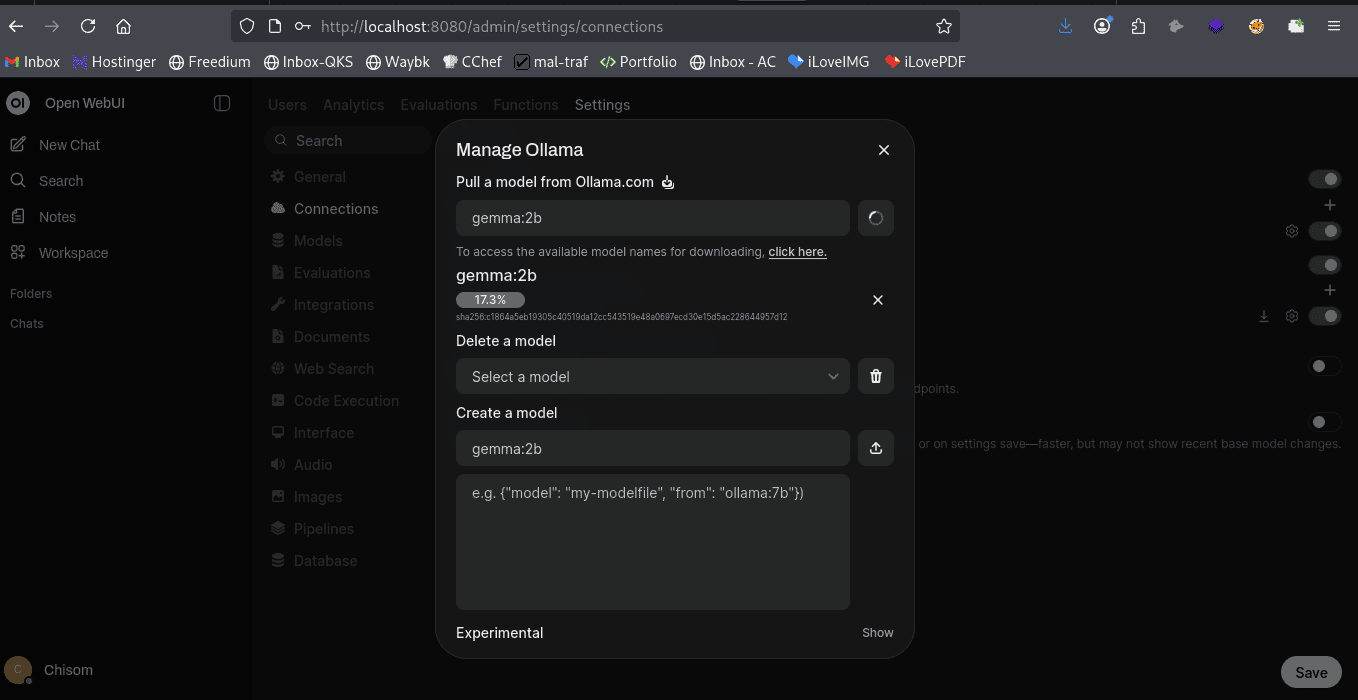
Today I spent time setting up a fully local AI environment using:
Instead of relying completely on cloud AI APIs, I’m experimenting with running AI models directly on my machine.
Why does this matter?
Because in cybersecurity, SOC operations, and penetration testing, data privacy and control are everything.
Imagine having an AI that can:
Analyze suspicious logs locally
Assist with malware analysis without sending data to external servers
Help automate SOC investigations
Generate detection rules for SIEM systems
Analyze configuration files or suspicious scripts safely offline
All without exposing sensitive infrastructure data to the internet.
This is where the industry is heading:
Private AI for Security Operations.
For organizations handling financial data, government systems, or internal infrastructure, local AI models will soon become a core security tool, just like firewalls and SIEM platforms.
As a System Administrator and Cybersecurity Engineer, I believe the next generation of defenders will combine:
And those who learn to build their own AI tools will have a serious advantage.
This is just the beginning of what I’m building in my lab.
Soon I’ll be experimenting with AI-powered tools for:
• SOC automation
• Threat hunting
• Bug bounty reconnaissance
• Malware behavior analysis
The future defender will not just use tools.
They will build them.
And that future is already here.
— Ali Chisom
Your email address will not be published. Required fields are marked *