I'm always excited to take on new projects and collaborate with innovative minds.
Lagos
I'm always excited to take on new projects and collaborate with innovative minds.
Lagos
A critical reminder that devastating breaches often stem from foundational security failures rather than exotic exploits.
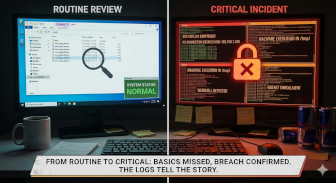
Recently, I analyzed a set of files retrieved from a server and what started as a routine review quickly turned into a confirmed security incident.
The artifacts revealed active exploitation, not a theoretical vulnerability.
Remote Code Execution (RCE) via exposed CGI/PHP endpoints
Malware delivery using wget, curl, and busybox
Presence of webshell backdoors (system(), shell_exec())
Evidence of Mozi & RedTail-style botnet malware
Hardcoded Command-and-Control (C2) IP addresses
Execution from /tmp, /var/tmp, and /dev/shm
Full server compromise
Potential botnet enrollment
Risk of data exposure, DDoS participation, and lateral movement
CVSS score in the critical range (≈ 9.8 – 10.0)
Most real-world breaches don’t start with “advanced zero-days.”
They start with:
Exposed services
Weak input validation
Lack of outbound traffic monitoring
Once command execution is achieved, everything else happens fast.
This analysis reinforced the importance of:
Egress filtering
Continuous monitoring
Treating “server artifacts” as incident evidence, not leftovers
Proper incident response timelines and IOC-driven detection
Security is not just about prevention — it’s about detection, response, and learning from real incidents.
If you’re in SOC, IR, blue team, or malware analysis, you know:
👉 The logs and files always tell a story.
This incident serves as a critical reminder that devastating breaches often stem from foundational security failures rather than exotic exploits. The presence of hardcoded C2 IPs and botnet artifacts underscores a rapid, automated attack chain that follows initial command execution. For defenders, the key takeaway is threefold: First, prevention must focus on basics—hardening exposed services and validating inputs. Second, detection is paramount; robust egress filtering and continuous monitoring of temporary directories and outbound connections are essential to catch post-exploitation activity. Finally, every artifact tells a story. Proactive, evidence-based analysis of server files and logs is not just maintenance—it's a core investigative function that transforms indicators into actionable intelligence, shortening response times and mitigating damage. True security resilience lies in learning from these incidents to bolster both defensive posture and investigative readiness.